|
|
@@ -0,0 +1,77 @@
|
|
|
+# A few common k8s secret types examples
|
|
|
+
|
|
|
+Here we will give some examples of how to work with a few common k8s secret types. We will give this examples here with the gcp provider (should work with other providers in the same way). Please also check the guides on [Advanced Templating](guides-templating.md) to understand the details.
|
|
|
+
|
|
|
+Please follow the authentication and SecretStore steps of the [Google Cloud Secrets Manager guide](provider-google-secrets-manager.md) to setup access to your google cloud account first.
|
|
|
+
|
|
|
+
|
|
|
+## Dockerconfigjson example
|
|
|
+
|
|
|
+First create a secret in Google Cloud Secrets Manager containing your docker config:
|
|
|
+
|
|
|
+
|
|
|
+
|
|
|
+Let's call this secret docker-config-example on Google Cloud.
|
|
|
+
|
|
|
+Then create a ExternalSecret resource taking advantage of templating to populate the generated secret:
|
|
|
+
|
|
|
+```yaml
|
|
|
+{% include 'gcpsm-docker-config-externalsecret.yaml' %}
|
|
|
+```
|
|
|
+
|
|
|
+This will generate a valid dockerconfigjson secret for you to use!
|
|
|
+
|
|
|
+You can get the final value with:
|
|
|
+
|
|
|
+```bash
|
|
|
+kubectl get secret secret-to-be-created -n <namespace> | -o jsonpath="{.data\.dockerconfigjson}" | base64 -d
|
|
|
+```
|
|
|
+
|
|
|
+## TLS Cert example
|
|
|
+
|
|
|
+We are assuming here that you already have valid certificates, maybe generated with letsencrypt or any other CA. So to simplify you can use openssl to generate a single secret pkcs12 cert based on your cert.pem and privkey.pen files.
|
|
|
+
|
|
|
+```bash
|
|
|
+openssl pkcs12 -export -out certificate.p12 -inkey privkey.pem -in cert.pem
|
|
|
+```
|
|
|
+
|
|
|
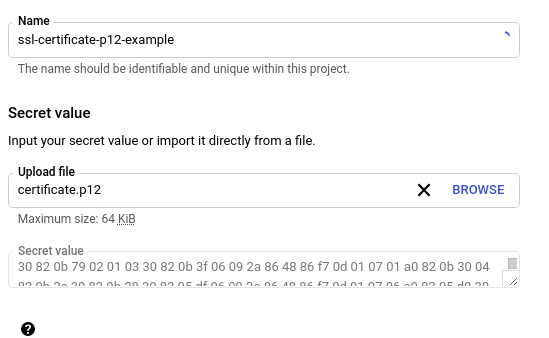
+With a certificate.p12 you can upload it to Google Cloud Secrets Manager:
|
|
|
+
|
|
|
+
|
|
|
+
|
|
|
+And now you can create an ExternalSecret that gets it. You will end up with a k8s secret of type tls with pem values.
|
|
|
+
|
|
|
+```yaml
|
|
|
+{% include 'gcpsm-tls-externalsecret.yaml' %}
|
|
|
+```
|
|
|
+
|
|
|
+You can get their values with:
|
|
|
+
|
|
|
+```bash
|
|
|
+kubectl get secret secret-to-be-created -n <namespace> | -o jsonpath="{.data.tls\.crt}" | base64 -d
|
|
|
+kubectl get secret secret-to-be-created -n <namespace> | -o jsonpath="{.data.tls\.key}" | base64 -d
|
|
|
+```
|
|
|
+
|
|
|
+
|
|
|
+## SSH Auth example
|
|
|
+
|
|
|
+Add the ssh privkey to a new Google Cloud Secrets Manager secret:
|
|
|
+
|
|
|
+
|
|
|
+
|
|
|
+And now you can create an ExternalSecret that gets it. You will end up with a k8s secret of type ssh-auth with the privatekey value.
|
|
|
+
|
|
|
+```yaml
|
|
|
+{% include 'gcpsm-ssh-auth-externalsecret.yaml' %}
|
|
|
+```
|
|
|
+
|
|
|
+You can get the privkey value with:
|
|
|
+
|
|
|
+```bash
|
|
|
+kubectl get secret secret-to-be-created -n <namespace> | -o jsonpath="{.data.ssh-privatekey}" | base64 -d
|
|
|
+```
|
|
|
+
|
|
|
+## More examples
|
|
|
+
|
|
|
+!!! note "We need more examples here"
|
|
|
+ Feel free to contribute with our docs and add more examples here!
|