Browse Source
Update IBM Cloud provider docs (#1614)
* update images and some wording * fix image filename * Update ibm-secrets-manager.md Signed-off-by: Idan Adar <iadar@il.ibm.com> Signed-off-by: Idan Adar <iadar@il.ibm.com>
16 changed files with 13 additions and 19 deletions
BIN
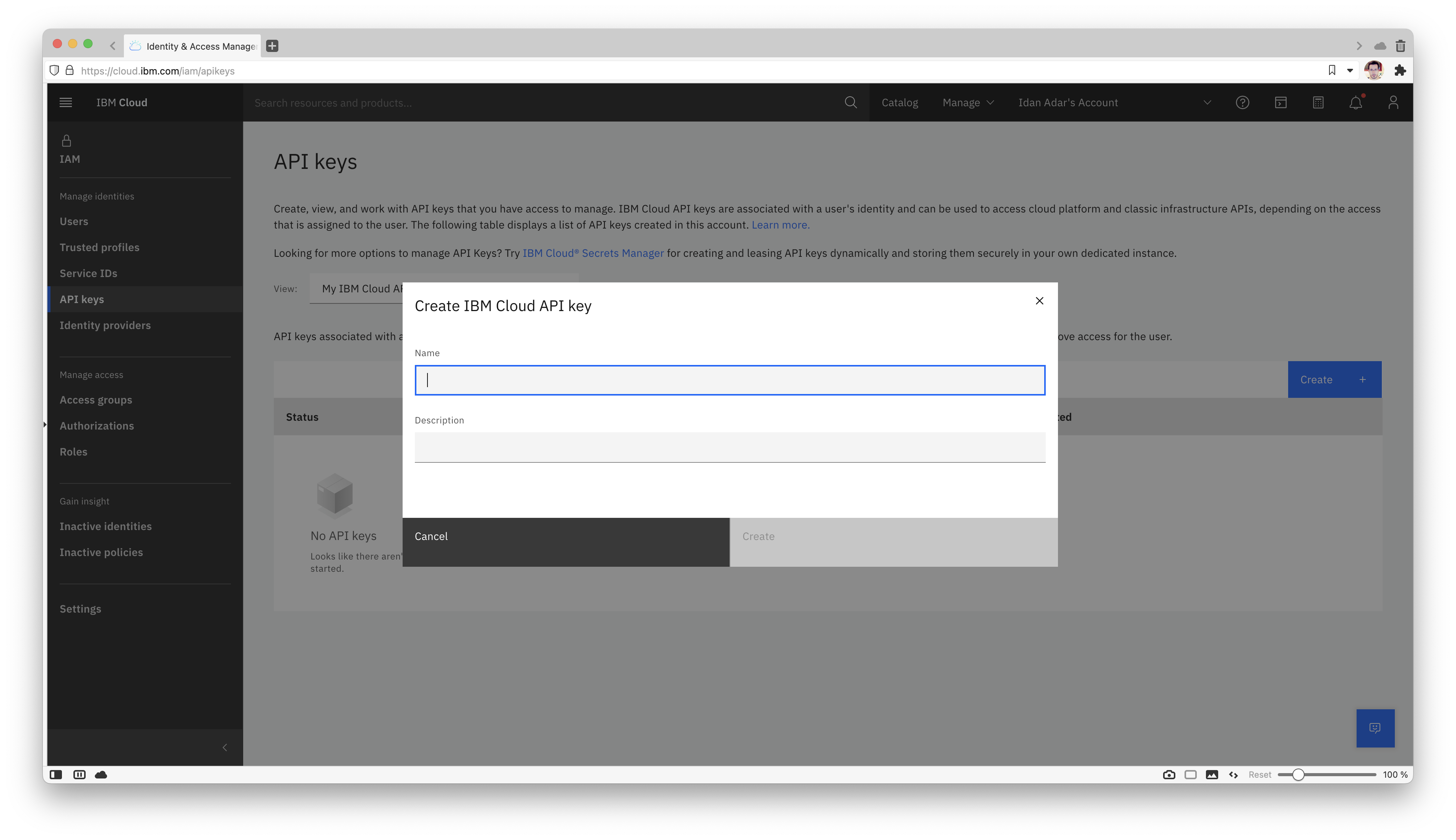
docs/pictures/screenshot_api_keys_create.png
BIN
docs/pictures/screenshot_api_keys_create_successful.png

BIN
docs/pictures/screenshot_api_keys_iam.png

BIN
docs/pictures/screenshot_api_keys_iam_left.png

BIN
docs/pictures/screenshot_container_auth_create_1.png

BIN
docs/pictures/screenshot_container_auth_create_2.png

BIN
docs/pictures/screenshot_container_auth_create_3.png

BIN
docs/pictures/screenshot_container_auth_create_group.png

BIN
docs/pictures/screenshot_container_auth_create_group_1.png

BIN
docs/pictures/screenshot_container_auth_create_group_2.png

BIN
docs/pictures/screenshot_container_auth_create_group_3.png

BIN
docs/pictures/screenshot_container_auth_create_group_4.png

BIN
docs/pictures/screenshot_container_auth_create_group_5.png

BIN
docs/pictures/screenshot_container_auth_iam_left.png

BIN
docs/pictures/screenshot_service_url.png

+ 13
- 19
docs/provider/ibm-secrets-manager.md
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||
|
||