doppler.md 3.3 KB
Doppler SecretOps Platform
Sync secrets from the Doppler SecretOps Platform to Kubernetes using the External Secrets Operator.
Authentication
Doppler Service Tokens are recommended as they restrict access to a single config.
NOTE: Doppler Personal Tokens are also supported but require
projectandconfigto be set on theSecretStoreorClusterSecretStore.
Create the Doppler Token secret by opening the Doppler dashboard and navigating to the desired Project and Config, then create a new Service Token from the Access tab:
Create the Doppler Token Kubernetes secret with your Service Token value:
HISTIGNORE='*kubectl*' kubectl create secret generic \
doppler-token-auth-api \
--from-literal dopplerToken="dp.st.xxxx"
Then to create a generic SecretStore:
{% include 'doppler-generic-secret-store.yaml' %}
NOTE: In case of a
ClusterSecretStore, be sure to setnamespaceinsecretRef.dopplerToken.
Use Cases
The Doppler provider allows for a wide range of use cases:
Let's explore each use case using a fictional auth-api Doppler project.
1. Fetch
To sync one or more individual secrets:
{% include 'doppler-fetch-secret.yaml' %}
2. Fetch all
To sync every secret from a config:
{% include 'doppler-fetch-all-secrets.yaml' %}
3. Filter
To filter secrets by path (path prefix), name (regular expression) or a combination of both:
{% include 'doppler-filtered-secrets.yaml' %}
4. JSON secret
To parse a JSON secret to its key-value pairs:
{% include 'doppler-parse-json-secret.yaml' %}
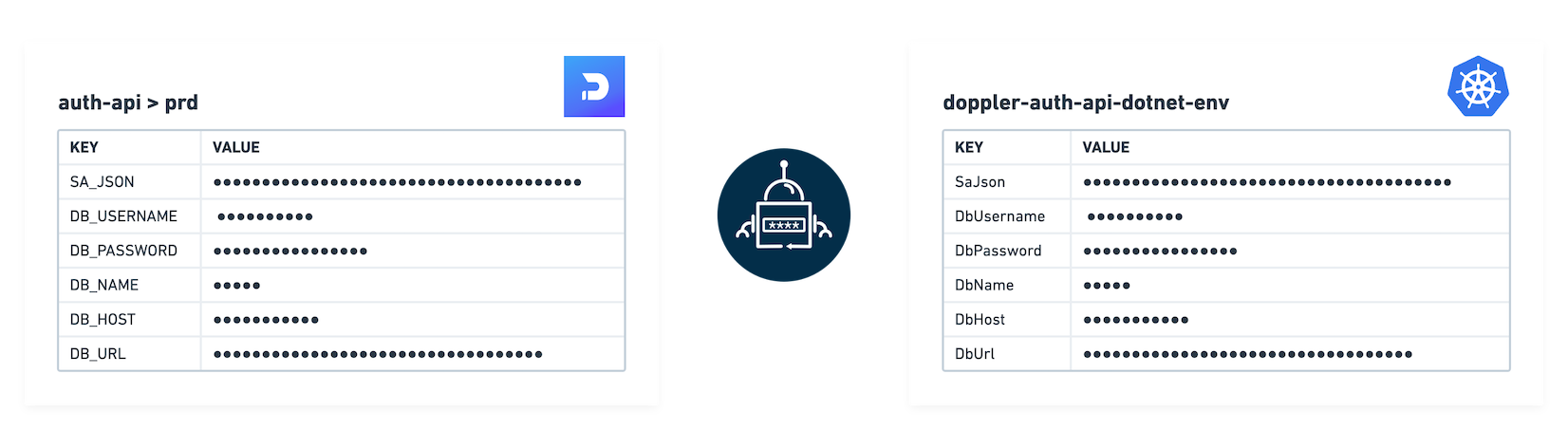
5. Name transformer
Name transformers format keys from Doppler's UPPER_SNAKE_CASE to one of the following alternatives:
- upper-camel
- camel
- lower-snake
- tf-var
- dotnet-env
- lower-kebab
Name transformers require a specifically configured SecretStore:
{% include 'doppler-name-transformer-secret-store.yaml' %}
Then an ExternalSecret referencing the SecretStore:
{% include 'doppler-name-transformer-external-secret.yaml' %}
6. Download
A single DOPPLER_SECRETS_FILE key is set where the value is the secrets downloaded in one of the following formats:
- json
- dotnet-json
- env
- env-no-quotes
- yaml
Downloading secrets requires a specifically configured SecretStore:
{% include 'doppler-secrets-download-secret-store.yaml' %}
Then an ExternalSecret referencing the SecretStore:
{% include 'doppler-secrets-download-external-secret.yaml' %}